Welcome to the third and final day of Pwn2Own Berlin 2026! Over the past two days, some amazing research has been put on display, and today looks just as intense. So far, we have awarded $908,750 for 39 unique zero days. With SharePoint and ESXi as targets today, the chances are excellent for crossing the million-dollar threshold. Here are the Master of Pwn standings as we begin the day:
Let's get to the results of Day Three:
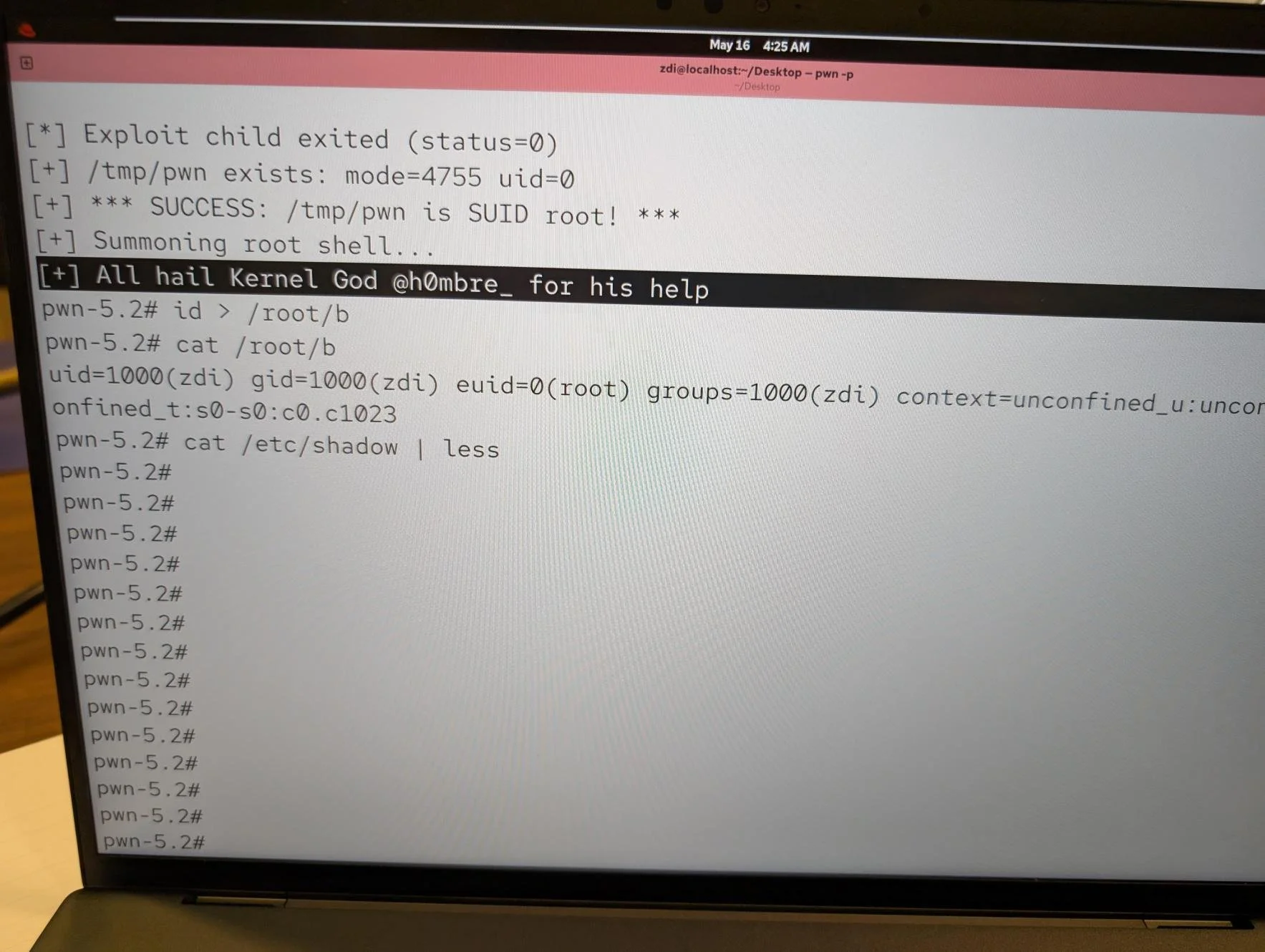
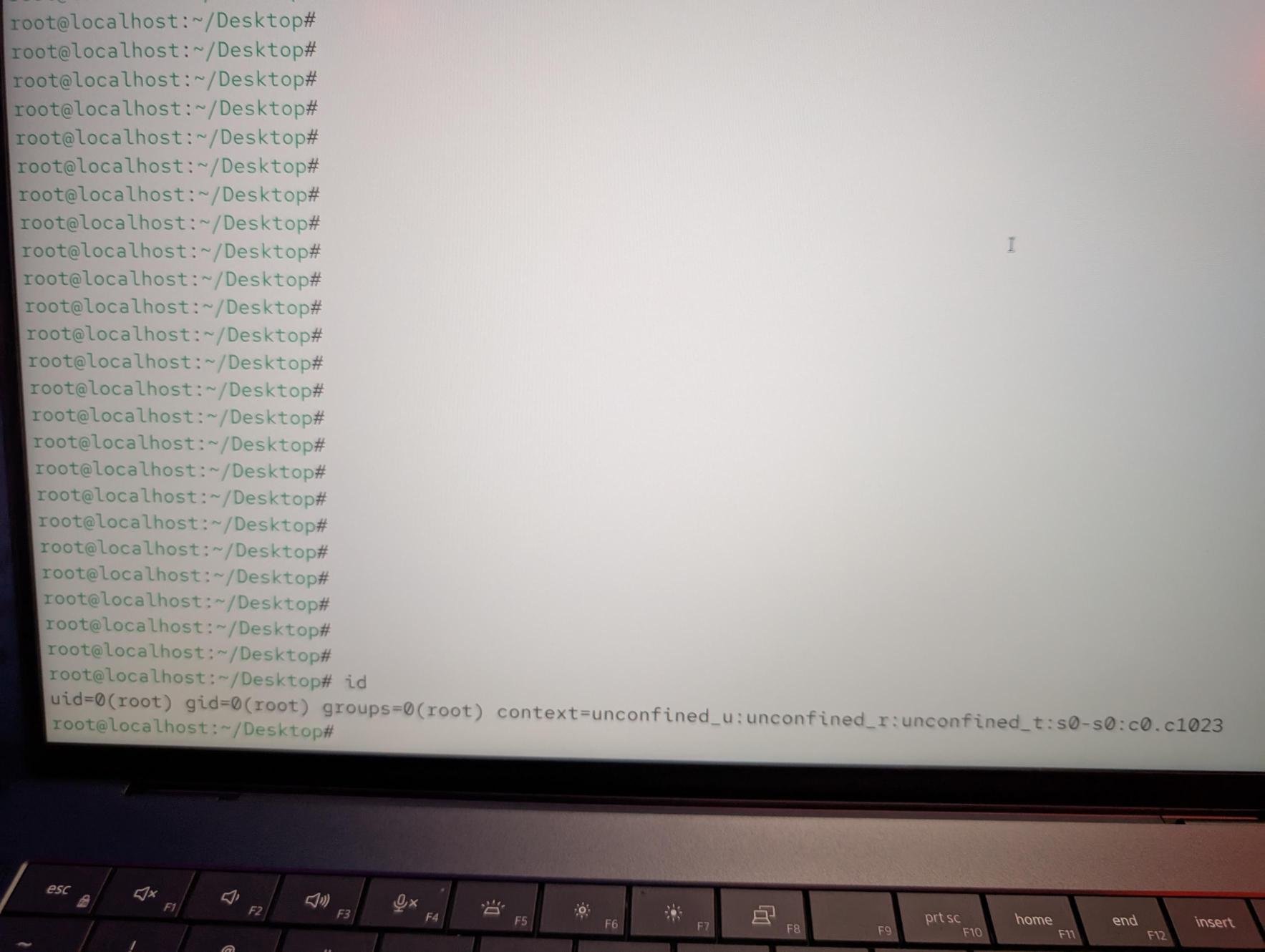
SUCCESS/COLLISION - Sina Kheirkhah (@SinSinology) of Summoning Team (@SummoningTeam) used two bugs to exploit Red Hat Linux, but one of the bugs was previously known. He still earns $7,000 and 1.5 Master of Pwn points.
SUCCESS - Le Tran Hai Tung (@tacbliw), dungnm (@dungnm_) and hieuvd (@gr4ss341) of Viettel Cyber Security (@vcslab) used an integer overflow to escalate privileges on #Windows 11. Their 5th round win nets them $7,500 and 3 Master of Pwn points.
SUCCESS - Satoki Tsuji (@satoki00) of Ikotas Labs, Inc. abused an external control to exploit OpenAI Codex and pop a host of calcs. He earns $20,000 and 4 Master of Pwn points.
FAILURE - Unfortunately, Giuseppe Calì of Summoning Team (@SummoningTeam) could not get their exploit of VMware ESXi working within the time allotted.
COLLISON - Although successful on stage, Emanuele Barbeno, Cyrill Bannwart, Yves Bieri, Lukasz D., Urs Mueller (@compasssecurity) of Compass Security targeted Anthropic Claude Code, hitting a one-vulnerability collision with a previous attempt and earning $20,000 and 2 Master of Pwn points.
SUCCESS - Hyunwoo Kim (@v4bel) chained a use-after-free and uninitialized memory bug to escalate privileges on Red Hat Enterprise Linux for Workstations in the fourth round, earning $5,000 and 2 Master of Pwn points.