Welcome to Day One of Pwn2Own Berlin 2026! Today, 22 entries take the Pwn2Own stage to target AI Databases, Coding Agents, Local Inferences, and a separate category for NVIDIA products, as the world’s top security researchers push technology to its limits. Exploits, surprises, and breakthrough discoveries are unfolding.
Follow the action live! We’ll be posting real-time updates and results throughout the competition on our blog and across social media. Stay up to date by following us on Twitter, Mastodon, LinkedIn, and Bluesky, and join the conversation using #Pwn2Own Berlin and #P2OBerlin for continuous coverage.
FAILURE - Unfortunately, Le Duc Anh Vu of Viettel Cyber Security could not get their exploit of OpenAI Codex working within the time allotted.
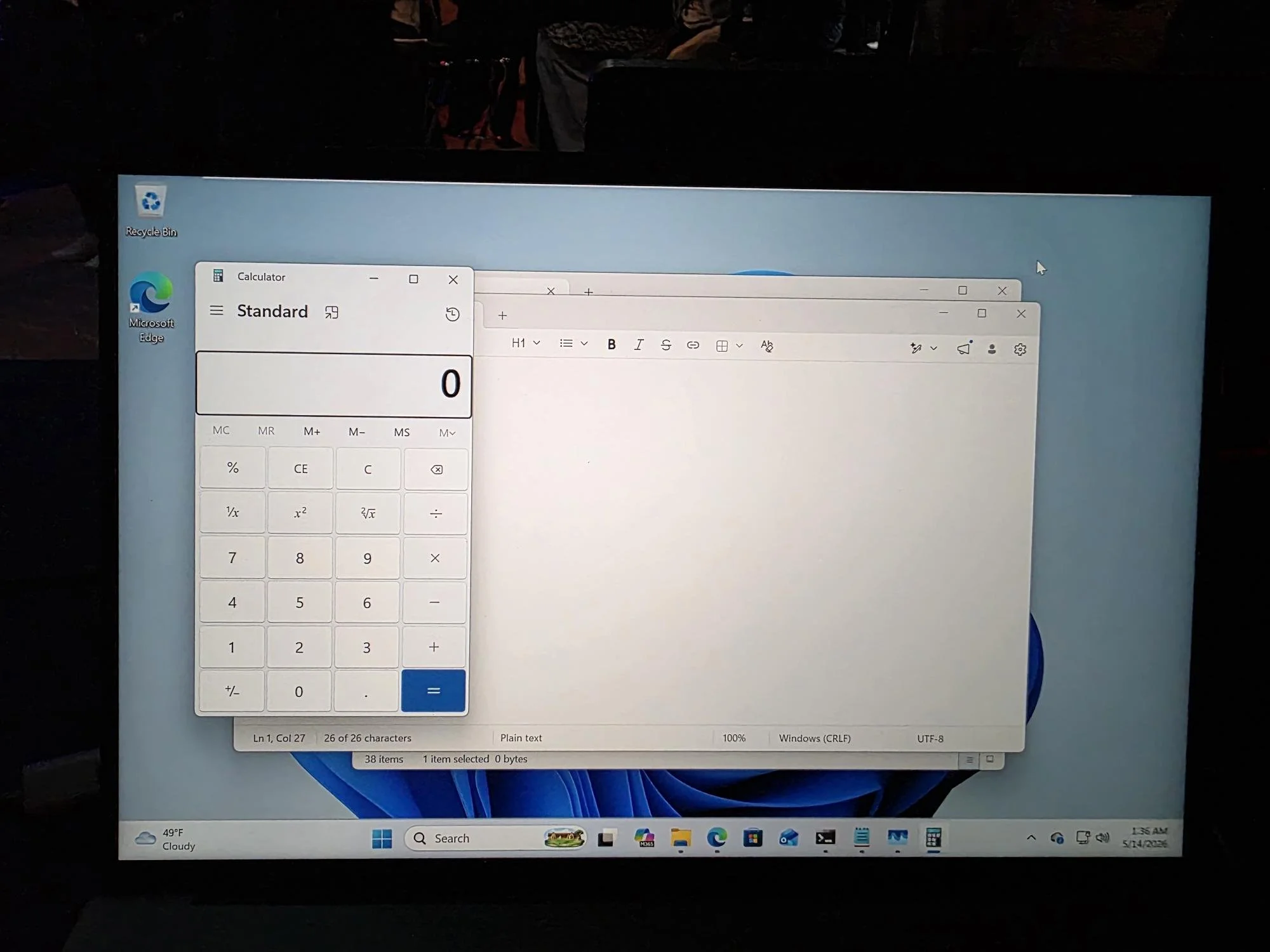
SUCCESS - Confirmed! Orange Tsai (@orange_8361) of DEVCORE Research Team (@d3vc0r3) chained 4 logic bugs to achieve a sandbox escape on Microsoft Edge, earning $175,000 and 17.5 Master of Pwn points.
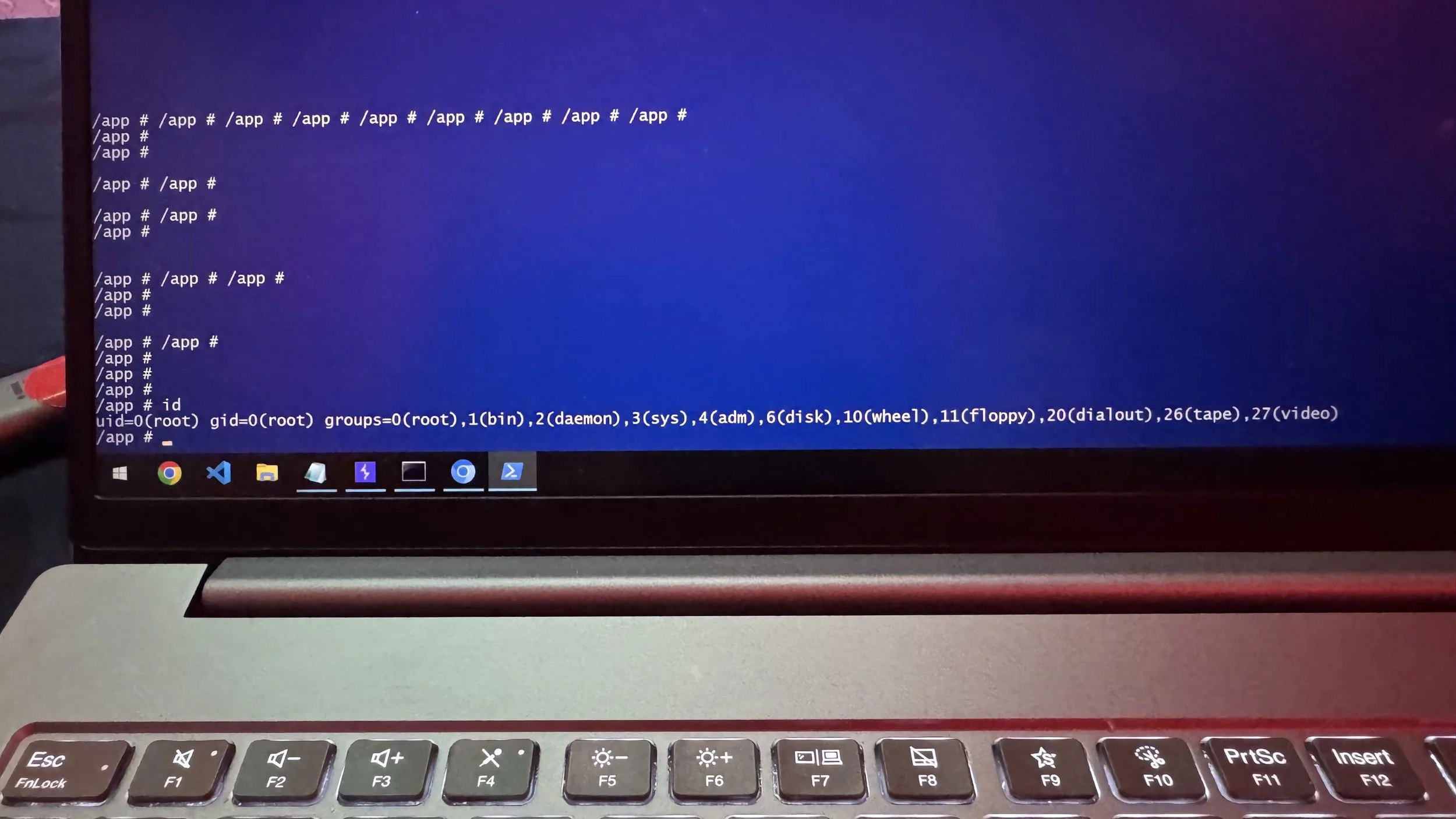
SUCCESS - Confirmed! chompie of IBM X-Force Offensive Research (XOR) used a single bug to exploit NV Container Toolkit, earning $50,000 and 5 Master of Pwn points.
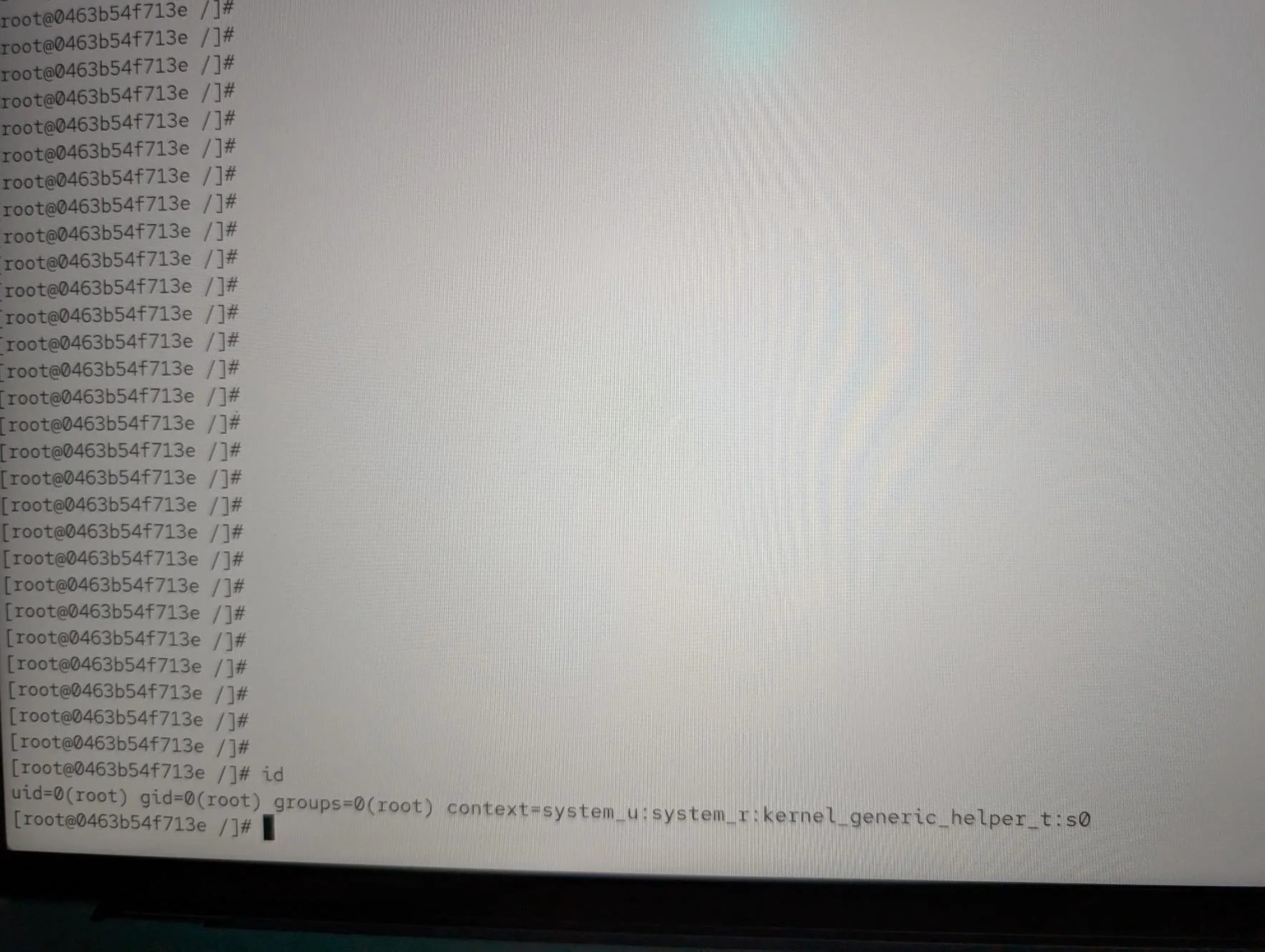
SUCCESS - Confirmed! k3vg3n chained 3 bugs including SSRF and Code Injection to take down LiteLLM. $40,000 and 4 Master of Pwn points. Full win.
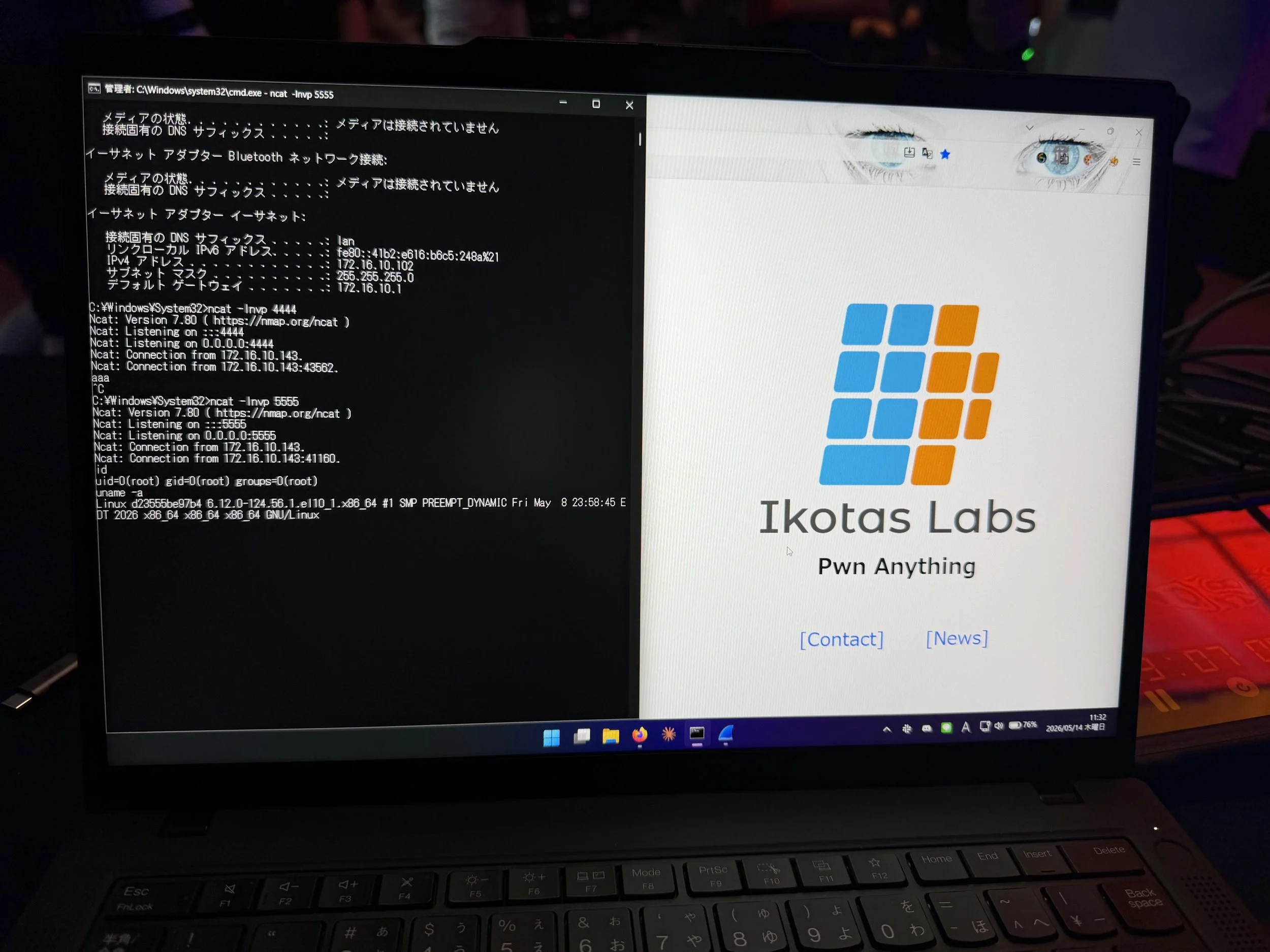
SUCCESS - Verified! Satoki Tsuji (@satoki00) of Ikotas Labs, Inc. used an Overly Permissive Allowed List bug to exploit NVIDIA Megatron Bridge, earning $20,000 and 2 Master of Pwn points.
FAILURE - Unfortunately, Park Jae Min could not get their exploit of Oracle Autonomous AI Database working within the time allotted. #Pwn2Own #P2OBerlin